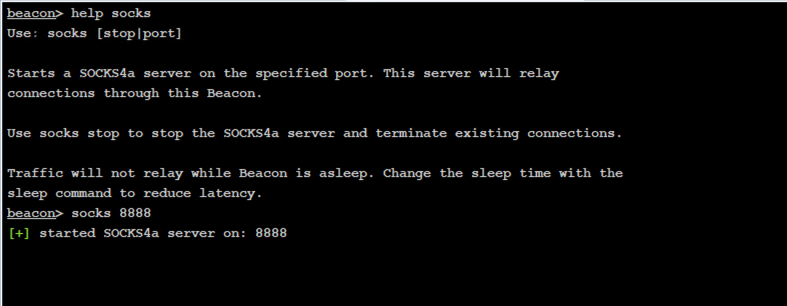
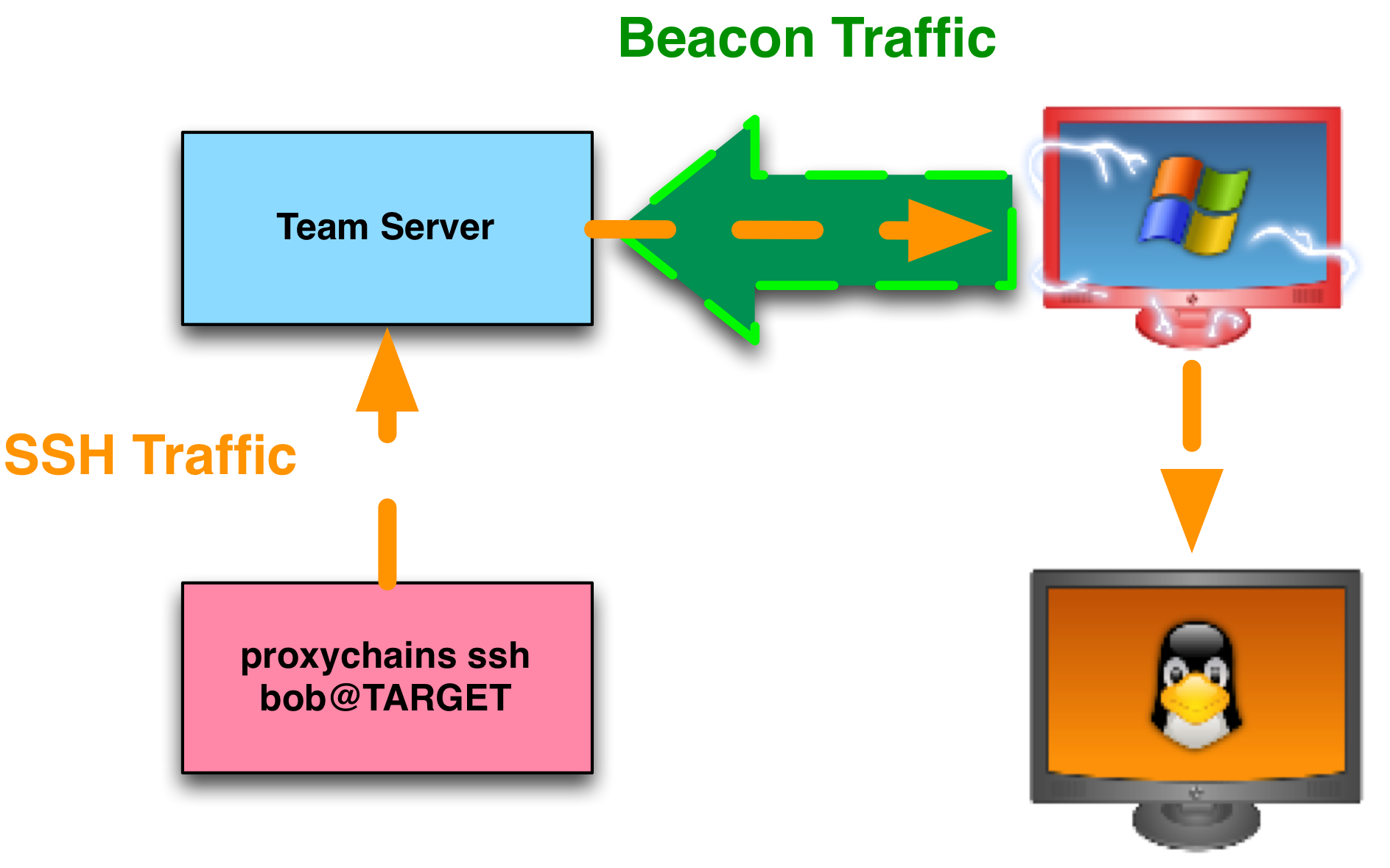
GitHub - Verizon/redshell: An interactive command prompt for red teaming and pentesting. Automatically pushes commands through SOCKS4/5 proxies via proxychains. Optional Cobalt Strike integration pulls beacon SOCKS4/5 proxies from the team server.
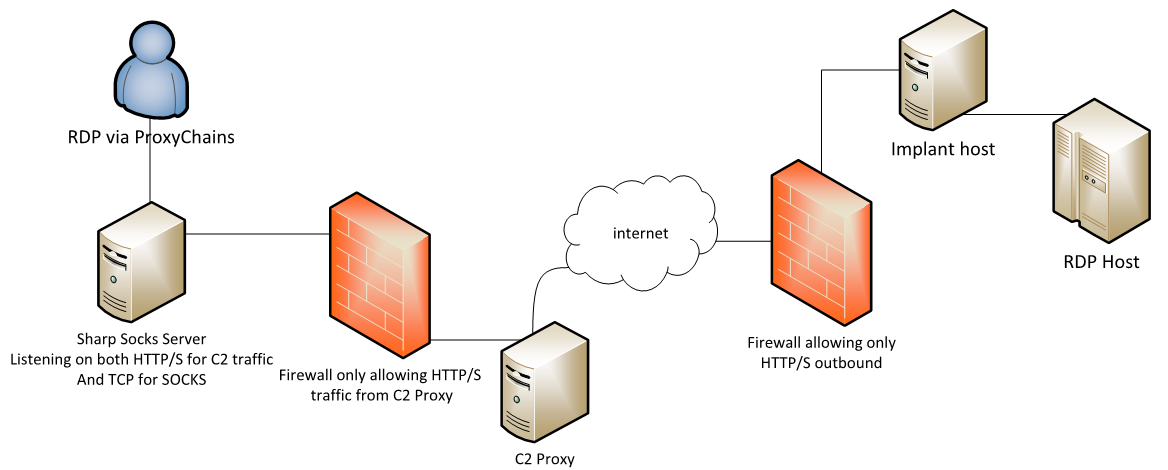
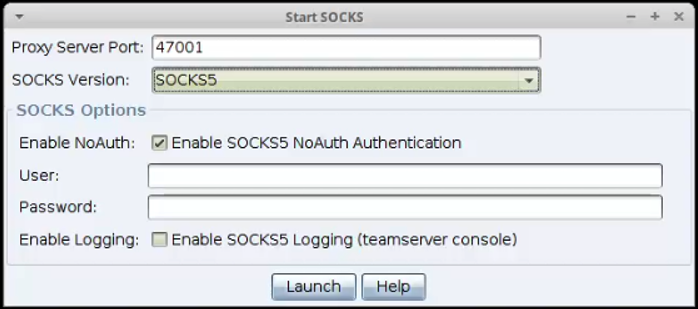
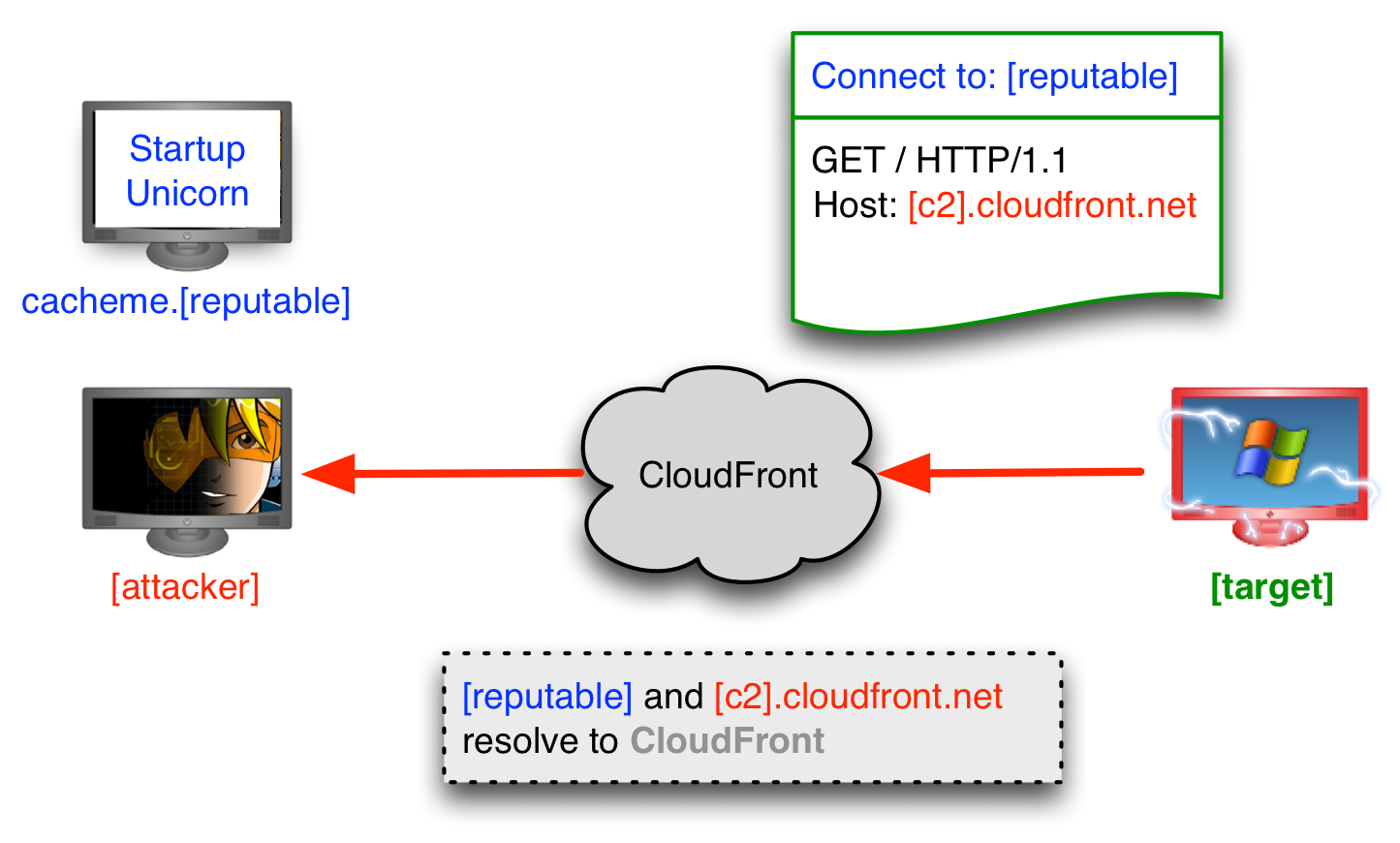
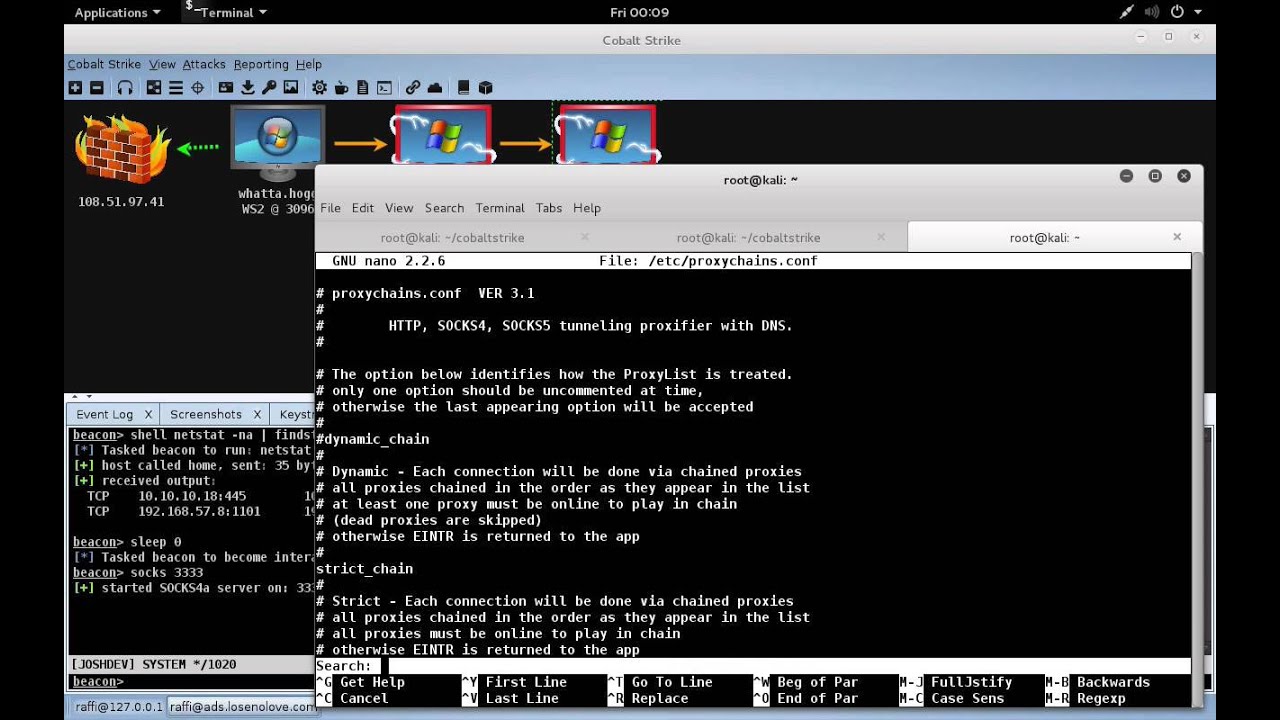
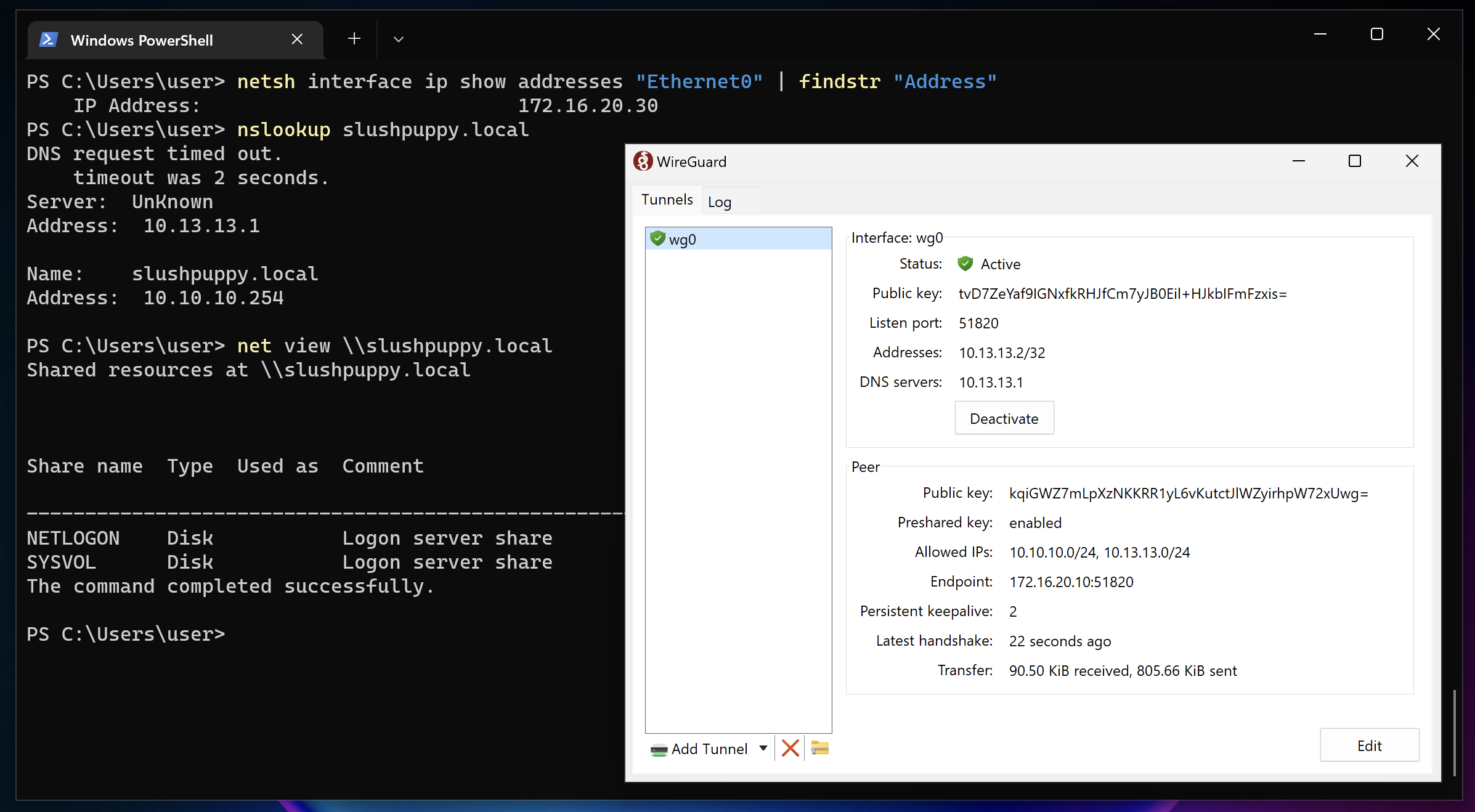
Proxy Windows Tooling via SOCKS. Leveraging SOCKS to proxy tools from a… | by Nick Powers | Posts By SpecterOps Team Members
Get Your SOCKS on with gTunnel. tl;dr: Steps to setup a wicked fast… | by Elliott Grey | Posts By SpecterOps Team Members